Web Supply Chain Risk in ANZ: Why the Browser is the New Front Line

Right now, code is executing in your users’ browsers that your WAF has never inspected, your DAST never tested, and your pen testers never touched. It’s not a gap in your tools, it’s a gap in where those tools look. And attackers have already found it.
● SAST and DAST to secure code
● EASM to identify exposed assets
● WAFs and bot mitigation to protect applications
● Regular penetration testing to validate risk
These controls have done their job well. But the application has moved. More of it now runs in the browser, shaped by a constantly changing ecosystem of third and fourth-party dependencies that these tools were never designed to see.
In many environments, this browser layer remains largely unmeasured. That is where web supply chain risk lives, and it is the front line security teams can no longer afford to ignore.
The Expansion of the Attack Surface
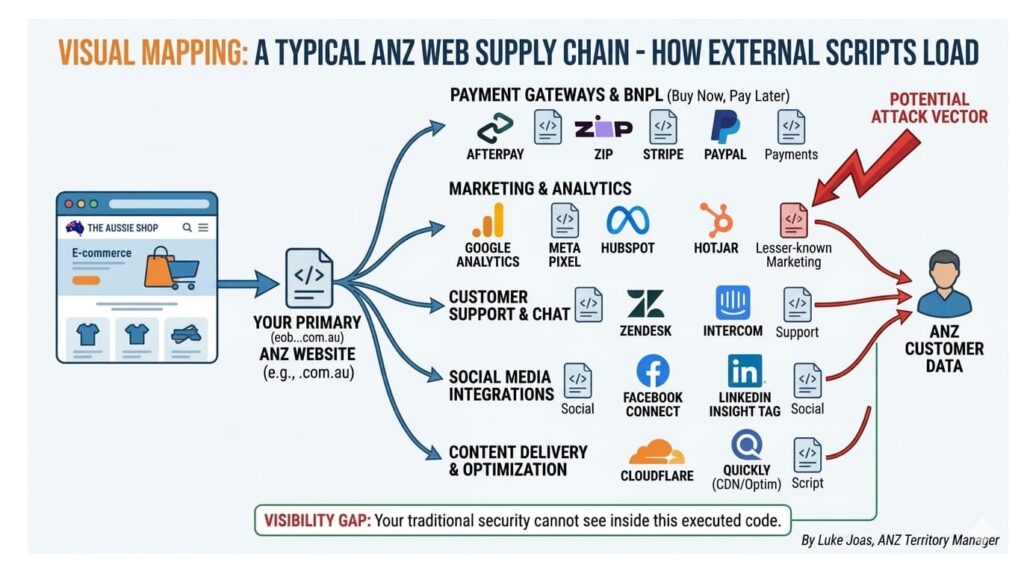
To support modern development and release cycles, applications rely heavily on a network of third and fourth-party technologies. Each introduces code that executes directly in the user’s browser, code the organisation did not write and often cannot see. Reflectiz research across 4,700 websites found that 64% of third-party applications access sensitive data without a clear business justification. Common examples include:
● Tag managers and marketing platforms
● Analytics and tracking technologies
● Embedded services and integrations
● Payment providers (e.g., Afterpay, Zip, Stripe)
The problem is not the vendors themselves, it is the lack of visibility into what they are actually doing at runtime.
Where Traditional Visibility Breaks Down
Most organisations have a clear view of what they build and deploy, but far less understanding of what actually executes in a real user session.
| Control | What it Sees | The “Browser Gap” (What it Misses) |
| SAST & DAST | First-party source code. | Runtime behavior of third-party scripts. |
| EASM | External IP assets and domains. | In-browser data interactions and data skimming. |
| WAF | Incoming traffic patterns. | Malicious logic running inside the browser. |
| Pen-Testing | A point-in-time snapshot. | Real-time changes in the third-party ecosystem. |
These controls operate outside the browser layer. The result is a gap between known vendors and actual runtime dependencies, and that is exactly where web supply chain risk sits.
The Rise of Web Supply Chain Risk in ANZ
This gap is becoming more critical as attackers move away from hardened infrastructure toward:
● Third-party script compromise
● Dependency hijacking
● Data exfiltration through browser-executed code
This is not theoretical. High-profile web skimming attacks, including incidents affecting major airlines, ticketing platforms, and retail brands globally, followed exactly this pattern: attackers compromised a trusted third-party script, injected malicious code into payment flows, and exfiltrated card data for months before detection. Traditional controls generated no alerts, because the attack never touched the infrastructure those controls monitor.
The Regulatory Stake
In Australia, the stakes have never been higher. The OAIC is increasingly focusing on how data is collected and handled in the browser. As outlined in Reflectiz’s analysis, misconfigured trackers can expose sensitive user data, with potential penalties reaching up to AUD $50 million or more.
Organisations are now strictly accountable for:
- What data is collected in the browser.
- Whether that aligns with user consent.
- Exactly where that data is being sent.
From Visibility to Context: The Next Phase of Attack Surface Management
Knowing what assets you have is no longer enough. The question security teams need to answer is: what are those assets doing? For web applications, that question cannot be answered from outside the browser. It requires continuous observation of what scripts are executing, what data they are touching, and where that data is going, in real user sessions, not synthetic scans.
This is the gap that Continuous Threat Exposure Management (CTEM) frameworks are designed to close, and the browser is where that gap is most acute for organisations operating modern web applications.
Bringing the Browser into Scope
ANZ organisations are already navigating this. Village Roadshow needed visibility across hundreds of client-side scripts to demonstrate PCI DSS compliance, a requirement that cannot be met by server-side tools alone. Lion faced the challenge of managing browser-side risk across a complex, distributed environment spanning multiple brands and teams. In both cases, the answer started with getting visibility into what was actually running in the browser.
To manage the web supply chain in practice, you must be able to:
● Continuously observe script execution across key user journeys.
● Identify when script behaviour changes in meaningful ways.
● Map data flows across third and fourth-party dependencies.
Final Thought
Modern web applications run on a shadow supply chain, dozens of third and fourth-party scripts executing in real user sessions, largely invisible to conventional security controls. The organisations that close this gap will not just reduce risk; they will be better positioned to meet the compliance and privacy obligations that regulators are increasingly enforcing. The ones that don’t are operating with an unknown variable at the heart of their application risk. It’s time to bring the browser into scope.

Luke Joas leads ANZ for Reflectiz, helping Australian and New Zealand enterprises secure their web supply chains and stay ahead of evolving privacy regulations. Reflectiz recently opened its Sydney office at Level 13, 333 George Street. Luke welcomes a conversation — reach him at [email protected].
FAQs
Does Reflectiz have an office in Australia?
Yes. Reflectiz has recently opened a brand new office in Sydney, Australia, establishing a local presence to serve Australian and New Zealand enterprises. The ANZ region is managed by Luke Joas, Reflectiz’s ANZ Regional Manager, who helps organizations in the region secure their web supply chains and meet evolving privacy regulations. You can reach Luke directly at [email protected].
How do web skimming attacks actually work, and have they affected major organizations?
Web skimming attacks follow a consistent pattern: attackers compromise a trusted third-party script, inject malicious code into payment flows, and silently exfiltrate cardholder data — often for months before detection. Because the attack executes entirely inside the browser, it never touches the server infrastructure that traditional security controls monitor, generating no alerts. High-profile incidents have affected major airlines, ticketing platforms, and retail brands globally. The attack succeeds not because of a weakness in the organization’s own code, but because of a lack of visibility into what trusted third-party scripts are actually doing at runtime
How does this relate to Continuous Threat Exposure Management (CTEM)?
CTEM is a framework for continuously identifying, assessing, and reducing exposure across an organization’s attack surface — moving beyond point-in-time assessments to an ongoing process. The browser layer represents one of the most acute gaps in CTEM programs for organizations running modern web applications, because it’s where the attack surface has expanded most significantly and where visibility has lagged furthest behind. Bringing the browser into scope for CTEM means shifting from a question of ‘what assets do we have?’ to ‘what are those assets actually doing?’ — a question that can only be answered through runtime observation.
How have ANZ organizations like Village Roadshow and Lion approached web supply chain security?
Both Village Roadshow and Lion serve as real-world examples of ANZ enterprises tackling browser-side risk. Village Roadshow needed visibility across hundreds of client-side scripts specifically to demonstrate PCI DSS compliance — a requirement that server-side tools alone cannot satisfy, since PCI DSS increasingly addresses what executes in the user’s browser during payment flows. Lion faced the challenge of managing browser-side risk across a complex, distributed environment spanning multiple brands and teams. In both cases, the starting point was the same: gaining clear visibility into what was actually running in the browser, before attempting to assess or remediate risk.
What are fourth-party dependencies, and why are they particularly difficult to manage?
Fourth-party dependencies are the scripts and services loaded by your third-party vendors — vendors of your vendors. When you embed a tag manager or analytics platform, that tool may itself load additional scripts from other providers, each with their own behavior, data access patterns, and potential vulnerabilities. Organizations often have no direct contractual relationship with these fourth parties and limited ability to audit their code. Yet those scripts execute in your users’ browsers with the same access to page data as your own first-party code. Mapping and monitoring these extended dependency chains is one of the core challenges of web supply chain security.
What are the regulatory consequences of browser-side data exposure in Australia?
Australian organizations face significant regulatory risk if sensitive user data is collected or transmitted through the browser without proper oversight. The Office of the Australian Information Commissioner (OAIC) is increasingly focused on how data is handled at the browser level. Misconfigured trackers can expose sensitive user data in ways that violate privacy obligations, with potential penalties reaching AUD $50 million or more. Organizations are now strictly accountable for what data is collected in the browser, whether collection aligns with user consent, and exactly where that data is being sent — all of which require runtime visibility to verify.
What does continuous monitoring of the browser layer actually involve in practice?
Continuous browser monitoring means observing what scripts are executing across real user journeys — not synthetic scans — and tracking what data those scripts touch and where it goes. In practice, it requires three core capabilities: continuously observing script execution across key user journeys (such as checkout flows and login pages); identifying when script behavior changes in meaningful ways, such as a previously trusted script suddenly accessing payment fields; and mapping data flows across third- and fourth-party dependencies to understand the full chain of data handling. This kind of monitoring cannot be replicated by server-side tools or periodic assessments because the threat environment changes continuously.
What is web supply chain risk, and why does it matter for ANZ organizations?
Web supply chain risk refers to the security threats introduced by third- and fourth-party scripts that execute directly in users’ browsers — code your organization didn’t write and often can’t see. Modern web applications depend on dozens of external technologies, from tag managers and analytics platforms to payment providers and embedded services. Reflectiz research across 4,700 websites found that 64% of third-party applications access sensitive data without a clear business justification. For ANZ organizations, this matters because attackers have shifted their focus away from hardened server infrastructure toward this largely unmonitored browser layer, where traditional security tools have no visibility.
What steps should security teams take to start addressing web supply chain risk?
The foundation is visibility. Security teams need to move beyond an inventory of known vendors to an understanding of what those vendors’ scripts are actually doing in real user sessions. Practically, this means establishing continuous observation of script execution across key user journeys, building a baseline of expected script behavior so anomalies can be detected when scripts change, mapping data flows across the full chain of third- and fourth-party dependencies, and aligning what is observed with user consent frameworks and regulatory requirements such as those enforced by the OAIC. Organizations that address this gap will not only reduce their exposure to web skimming and data exfiltration attacks, but will also be better positioned to meet the privacy and compliance obligations that Australian regulators are increasingly enforcing.
Why can’t my existing security tools (WAF, SAST, DAST, pen testing) protect against browser-side threats?
Each of these tools is designed to inspect a different part of your environment — and none of them looks inside the browser at runtime. SAST and DAST examine your first-party source code but miss the runtime behavior of third-party scripts. WAFs monitor incoming traffic patterns but cannot see malicious logic executing inside the browser. EASM identifies external IP assets and domains but doesn’t capture in-browser data interactions or skimming. Penetration testing provides a point-in-time snapshot but can’t track real-time changes in the third-party ecosystem. The result is a structural visibility gap at exactly the layer attackers are now targeting.
Subscribe to our newsletter
Stay updated with the latest news, articles, and insights from Reflectiz.
Your Website looks great!
But what’s happening behind the scenes?
Discover your website blind spots and vulnerabilities before it’s too late!







