New Guide
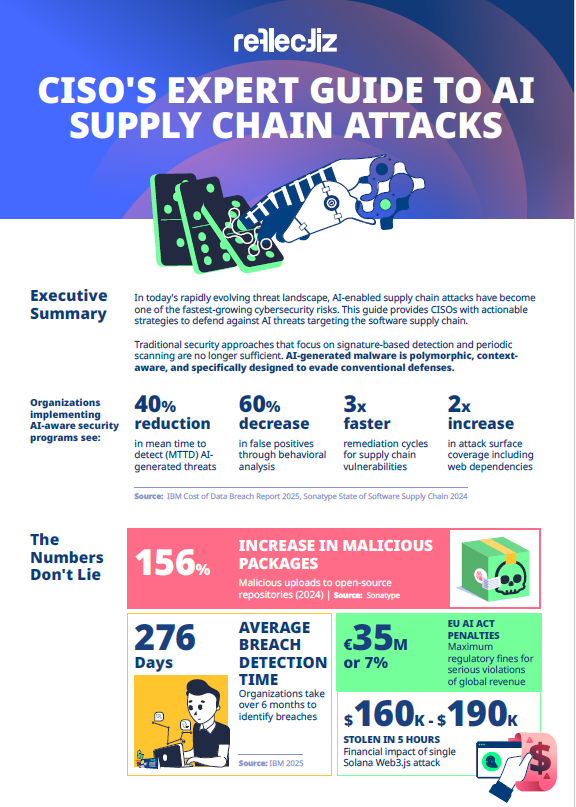
CISO’s Expert Guide to AI Supply Chain Attacks
Get your FREE GUIDE

AI-enabled supply chain attacks jumped 156% last year. Discover why traditional defenses are failing and what CISOs must do now to protect their organizations.
Here’s what makes AI-generated malware genuinely different:
- Polymorphic by default: Like a virus rewriting its own DNA, each instance is structurally unique with the same malicious purpose.
- Context-aware: Modern AI malware includes sandbox detection worthy of a paranoid programmer. One sample waited for Slack API calls and Git commits, signs of a real dev environment, before activating.
- Semantically camouflaged: Malicious code masquerades as legitimate functionality. Backdoors disguised as telemetry modules, complete with documentation and unit tests.
- Temporally evasive: Some variants lie dormant for weeks or months, waiting for triggers or simply outlasting security audits.
[Excerpts from the full guide]
Download the full guide for more >>
Take control
Stay up to date with the latest news and updates