Act Now: PCI DSS v4 Deadline Approaching Fast
Exclusive Interview with Senior PCI DSS Consultant, Stuart Golding
The current version of PCI DSS expires on March 31st, 2024 – Are you ready for the new version? Reflectiz conducted an in-depth interview with Stuart Golding, a seasoned PCI DSS consultant, discussing the main challenges organizations face as they prepare for PCI DSS v4.
In this interview, Stuart Golding delves into the intricate details of the new requirements introduced in PCI DSS version 4, shedding light on how they differ from previous versions and the implications for organizations. Drawing from his extensive experience as a seasoned PCI DSS consultant, Golding offers valuable insights and practical advice on tackling the complexities of PCI compliance. From understanding the technical nuances to addressing resource allocation challenges, Golding’s expertise provides a roadmap for organizations striving to meet the rigorous standards of PCI DSS v4.
But first –
What is PCI DSS?
PCI DSS [Payment Card Industry Data Security Standard] is a set of security standards designed to ensure that all companies that accept, process, store, or transmit credit card information maintain a secure environment. Every online business with payment pages should obtain the PCI DSS v4 checklist, and make sure the business comply with new sections, such as sections 6.4.3 and 11.6.1.
About Stuart Golding
Stuart Golding brings nearly 15 years of expertise in PCI DSS consultancy, having begun his journey with B&Q in the United Kingdom, where he assisted in establishing PCI DSS compliance protocols. Since then, he has worked with prominent retail giants such as WH Smith, Sainsbury’s, Argos, New Look, and Nintendo, guiding them through the intricacies of PCI DSS compliance. His extensive experience encompasses conducting gap analysis, interpreting compliance requirements, and facilitating implementation. Additionally, Stuart has conducted PCI DSS assessments from a merchant’s perspective.
An in-depth interview with Stuart Golding
Hi Stuart, good to have you here. Can you provide an overview of the new requirements outlined in PCI DSS v4?
Thank you for having me. PCI DSS v4 aligns more closely with ISO 27001, which promotes compatibility with other information security standards. There’s a significant emphasis on continuous compliance, moving away from the once-a-year approach. The new version introduces requirements that necessitate ongoing assessment and accountability. Every requirement now explicitly requires that organizations define who is responsible for compliance, emphasizing continual monitoring and management throughout the year. Moreover, PCI DSS v4 incorporates more technical requirements to address evolving cybersecurity threats, ensuring the industry remains proactive in safeguarding cardholder data.
How do these requirements differ from previous versions of PCI DSS, particularly concerning the management of payment page scripts?
There’s a much greater technical emphasis in PCI DSS v4 compared to v3, which had benefited from updates up to v3.2.1, but it is now very outdated. The new version reflects advancements in technology, particularly in payment methods like tablets and mobile phones. It introduces explicit future dated requirements regarding payment page scripts, which were absent in previous versions. These requirements are crucial, hence their deferral until March 2025 to ensure proper implementation. Until then, these specific web monitoring requirements are still considered best practice.
What do you see as the main challenges for organizations to implement the new PCI DSS v4 requirements?
The primary challenge lies in resource allocation, including time and cost. Implementing version 4 will undoubtedly incur additional expenses. Organizations that have outsourced most of their PCI DSS scope to validated third party payment service providers will fare better, as they can delegate many new requirements to their contracted service providers, such as iFrame and hosted payment page providers. Those who handle compliance internally, especially in online environments, may face greater challenges. It’s advisable for such organizations to reconsider their strategy and potentially outsource more elements to validated third-party payment service providers.
You mentioned the payment gateway iFrames. What exactly changed regarding activity through iFrames, and what are the main challenges?
There’s nothing explicitly mentioned about iFrames in the requirements, but there are more specific requirements around managing payment page scripts and consumer browsers, and dealing with issues that hackers have exploited to obtain payment card data. The standards now emphasize that we need more than just the hosted payment page or the iFrame to be absolutely secure. We need to monitor how the payment page appears when it reaches the consumer’s browser, because there are identified risks. Some major data breaches have occurred due to these risks.
For organizations that haven’t implemented the new requirements yet, what steps should they take?
PCI DSS version 3.2.1 retires at the end of March 2024, meaning organizations must act promptly to comply with version 4, while some may have recently re-attested against version 3.2.1, and they still have up to a year from the anniversary of their last re-attestation to implement mandatory v4 requirements giving themselves some contingency time. However, those who haven’t started planning may find themselves falling behind. It’s crucial to initiate planning and implementation promptly, considering the time and resources required. Waiting until the last minute could jeopardize compliance efforts and leave organizations vulnerable to security risks; remember, vulnerabilities and risks the new requirements seek to protect organizations from, are real and exploitable now.
New Sections 6.4.3 and 11.6.1
How does a big organization prepare for the new sections 6.4.3 and 11.6.1?
Organizations will need to devise strategies to address these new obligations. My advice would always lean towards outsourcing to experts in the field. That’s why I’ve consistently advocated for solutions like hosted payment pages and iFrames, where the responsibility for cardholder data is entrusted to competent organizations with validated solutions. Hence, organizations should explore alternatives like Reflectiz. They need to grasp what solutions are available, who can provide assistance, and understand the implementation requirements. Structured projects need to be initiated to prepare for the March deadline next year. This preparation entails thorough business analysis. It’s not just about implementing monitoring software; it’s about having the necessary backend teams to interpret the monitoring data and take appropriate actions. This integration will inevitably involve departments such as marketing, which may not have previously considered PCI DSS compliance. They will now be accountable, especially in identifying and rectifying any issues related to payment page scripts and JavaScript. Therefore, there will be an expanded scope of responsibility, requiring remediation and mitigation efforts across various departments.
Some solutions offer embedded scripts for monitoring, while others provide remote monitoring solutions. Which one do you think is better?
I believe the choice between embedded and remote monitoring depends on each merchant and how they configure their web page. It’s about understanding the benefits of each solution and what additional value they bring beyond PCI DSS controls. When selecting the right solution, organizations should consider the broader advantages they offer and what they can gain from their investment. Personally, I tend to favor solutions that are least intrusive, both in terms of cost and implementation. These solutions typically require minimal development or changes to the organization’s web page, allowing for quick implementation and results. Given that these requirements which are considered best practice until March 2025 pose real risks to organizations now, the sooner these controls are implemented the better. Major data breaches have already occurred due to these vulnerabilities, highlighting the importance of prompt action. Therefore, I advise organizations to make informed decisions swiftly, implementing solutions promptly rather than waiting until the last minute.
Regarding the activation of change and tamper detection mechanisms in section 11.6.1, could you explain its significance?
This requirement addresses web pages that rely on assembling active content, primarily JavaScript, from various internet sources. Given the dynamic nature of web content management systems, detecting changes or malicious activities solely through traditional methods is challenging. Monitoring must occur in real-time as the page is constructed and JavaScript is interpreted in the consumer’s browser. This ensures timely detection of any malicious scripts or activities, enhancing overall security.
What are the common challenges organizations face in implementing change and tamper detection mechanisms?
Implementing these mechanisms can be daunting, especially for organizations lacking in-house expertise. Creating monitoring solutions internally may prove onerous and complex, particularly without the necessary skills. Additionally, understanding the long-term implications and resource requirements is crucial. Organizations must allocate sufficient time, budget, and manpower to meet the March 2025 deadline effectively. Furthermore, engaging stakeholders from various departments, including marketing, in understanding and addressing these requirements is essential. Overall, there will be a significant impact on resources and processes, requiring careful planning and execution to ensure compliance and security.
Finding New Solutions For The New Sections
The sections addressed by Reflectiz are 6.4.3 and 11.6.1, which are new requirements that companies previously did not have to address. Now, companies not only need to find solutions to meet these requirements but also often need to seek out new vendors to provide these solutions. Do you view this as a challenge? How do companies navigate finding new solutions for these types of requirements that they now need to address?
Yes, it can be a problem. When it’s a new solution, something people haven’t had to deal with before, we have to look further afield for solutions. So, we’ve met with Reflectiz and other potential solution providers at events focused on PCI DSS. Most organizations are aware of these resources and know they can attend such shows and forums. Additionally, there are support structures available, including different conferences like PCI London and groups such as the UK Merchants Payments Working Group. There’s also Vendorcom, an organization which focuses on payments and associated technologies. Most organizations have access to these resources or can seek guidance from peers, PCI DSS consultants, qualified security assessors, and their acquiring banks, which contractually require PCI DSS compliance. Tier two and tier one merchants are particularly familiar with these opportunities and can leverage them for help and advice.
From your experience, if a company does not comply with PCI DSS, what are the consequences?
Well, every organization with a contract with an acquiring bank is contractually obligated to be PCI DSS compliant, particularly level one and level two merchants. Level three and level four merchants, the smaller ones, tend not to be as heavily enforced by acquiring banks, but they should not avoid PCI DSS compliance, because they get hacked too. The larger merchants pose a bigger risk, so they tend to be the primary focus of acquiring banks. However, non-compliant organizations risk the security of the cardholder data they handle. While compliance doesn’t guarantee protection against breaches, it ensures the implementation of controls to prevent them. Compliance needs to be continuously maintained, as emphasized in PCI DSS v4, moving away from the previous annual certification model. Controls must be managed throughout the year to effectively mitigate risks and maintain security.
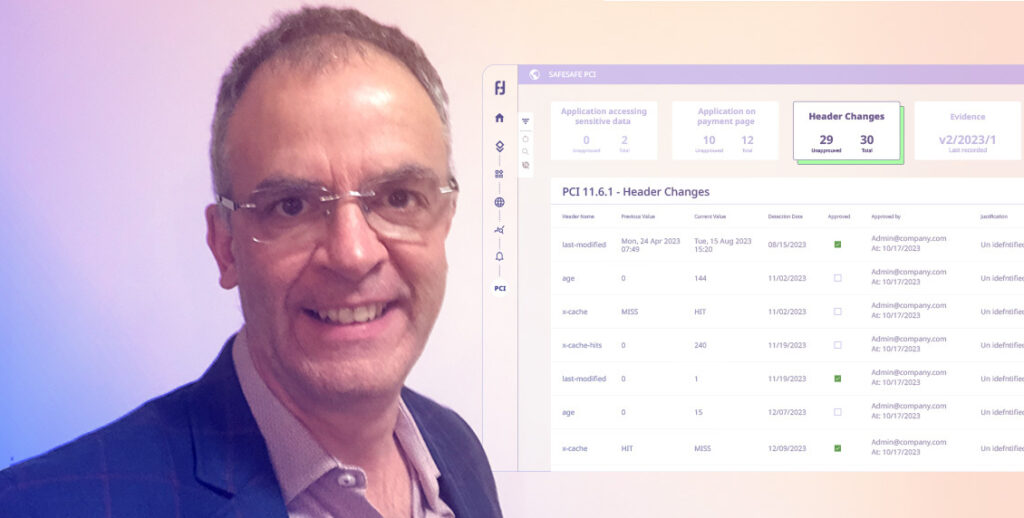
A Dedicated PCI Dashboard
The current version of PCI DSS expires on March 31st, 2024! Are you ready for the new version? Get full coverage on sections 6.4.3 and 11.6.1 with a dedicated PCI Dashboard to continuously meet the new requirements of PCI DSS v4, including reports! Click here
Subscribe to our newsletter
Stay updated with the latest news, articles, and insights from Reflectiz.
Your Website looks great!
But what’s happening behind the scenes?
Discover your website blind spots and vulnerabilities before it’s too late!







