The SolarWinds Supply Chain Attack: Implementing a Layered Security Approach

Updated on Aug 2nd, 2022
The recently exposed SolarWinds supply chain attack is one of the biggest cybersecurity events in recent memory. It created a ripple effect that will be felt for years to come on a global scale. Third-party security will never be the same again after this mega-breach, which affected some of the biggest Fortune 500 companies and US government entities. Let’s dive into the details.
SolarWinds is a Network Management System (NMS), a software vendor that gives companies the ability to monitor and examine their networks in greater detail. This renowned vendor fell prey to a software supply chain attack. In the Solarwinds supply chain attack, hackers gain unauthorized access to multiple companies – and in this case the most ironic one was probably FireEye, a leading cybersecurity firm.
What Exactly Happened on the SolarWinds Supply chain attack?
The culprit? Orion. This proprietary software created by SolarWinds is currently helping over 30,000 companies from around the world manage their IT resources and streamline their operations. All Orion software updates from around March 2020 were contaminated due to malware that was planted on the SolarWinds servers.
This means that some SolarWinds clients were unknowingly implementing infected software for many months and putting their data at risk. This malicious code, which took months to be detected, created a backdoor to several companies. Some of the potential victims include Microsoft, Cisco, Intel, Deloitte, and even some parts of the Pentagon. This list of targets can show you how a seemingly small malware attack can be scaled to the extent of a Nation State attack impacting government agencies.
The extent of the data theft caused by the Orion compromise is yet to be determined, but many experts are estimating that it could be 100 million data records.
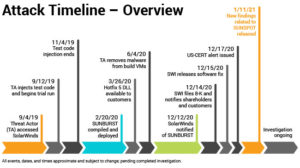
SolarWinds attack timeline. Source: The SolarWinds Blog
The Wider Risk in Digital Ecosystems
The biggest takeaway from this whole incident – third-parties have become an integral part of website ecosystems. These applications save time, cost and resources. However, as evident in the SolarWinds supply chain attack, they also allow hackers to exploit vulnerabilities that can be seriously tough to detect.
To understand how broad the risk is, here is another example. Ticketmaster UK was exposed after a third-party chatbot plugin called Inbenta went rogue and was exploited over a series of months. The result – a hefty £ 1.25 million fine by the Information Commissioner’s Office (ICO).
Not implementing a layered security approach can damage your business on multiple fronts. First, your organization bleeds money in real-time, with dev and security teams scrambling to solve the problem. Second, there is no knowing the hacker’s motivations. How much data has leaked and what will be done with this data is anyone’s guess. It’s crystal clear that software supply chain attacks and third-party risks can’t be ignored anymore.
Don’t Become The Next SolarWinds
What happens with software supply-chain attacks is no different from website third-party application attacks. The rapid digitalization of eCommerce, banking, finance, insurance, and eService websites has led to a huge reliance on third-party digital applications. This is creating numerous security risks and regulatory concerns.
In fact, the SolarWinds attacks caused governments to put the way that software is secured firmly under the spotlight, and has led to new regulations such as SBOM, the Software Bill of Materials, led by President Biden’s cybersecurity executive order. An SBOM is regulation that mandates a complete inventory of all the open source and third party components of any codebase, as well as licenses and patch status. While for organizations who do business with the government, an SBOM is an essential regulatory standard, the process is quickly becoming best practice across all tech industries to allow security teams to isolate and mitigate any security risks that may arise with a third-party product or solution.
Software supply chain attacks, triggered by third-parties can happen to your website. Even more dangerous than the SolarWinds case, your third-parties can be updated and manipulated remotely, making it even more difficult to contain their behavior and monitor their activities. Once they go rogue, hackers can access and harvest data for criminal use. Just ask Ticketmaster UK.
Learn more about The Cybersecurity Effects of Fourth-Parties
Companies from multiple sectors are experiencing the negative impact of this lack of visibility into third-party web apps. The threats that are created by updates and changes are simply out of their jurisdiction. Security teams are therefore having a tough time addressing the associated security and regulatory risks.
The solution? You simply have to consider third-party applications as an integral part of your ecosystem and treat them accordingly. That means you need to monitor them on an ongoing basis to see if anyone is making changes to code and understand what the impact of that is on your security and regulatory posture.
Can SolarWinds happen again? Is your website a third-party software supply chain attack risk? The answer to these questions is YES.
Your Traditional Security Toolbox is Not Enough
How can you take care of security blind spots in your third-party ecosystem, to avoid threats such as types of malware infecting your users, identity theft, or a data breach resulting in the loss of customer information?
Security blind spots are undetected gaps that exist between your application security processes and the security risks created by third-parties. Just like the SolarWinds’ Orion vulnerability opened up thousands of hacking options for any threat actor who wanted to take advantage, the modern website is no different. Traditional security solutions such as antivirus software or network security tools are simply incapable of handling this complex situation. The software supply chain attack needs something different.
The average website today has over 50 third-party applications running on it at any given time, just like Orion in the SolarWinds case. Simply knowing the operational status of these apps, and performing the occasional risk-assessment is not enough to eliminate the security blind spots they create.
Third-party apps on websites
To avoid being the next SolarWinds, you need an additional layer of security. You need to know that you’re managing a secure and compliant ecosystem by continuously monitoring of your third-parties. This is something the traditional tools can’t deliver, as they have their own roles – such as being a password manager, looking out for a traditional computer virus, or scanning on-premises network devices.
Even when you get more granular into application security, the average AppSec toolkit will help you monitor networks, implement security policies, and enforce whitelisting/blacklisting. Traditional tools also primarily provide static outputs for performance management, which isn’t enough. The same applies to third-party risk assessment solutions, which just score vendors and provide risk levels, without doing much on the governance front.
How to Control the Third-Party Apps on Your Website?
The bottom line is clear – third-party applications are providing threat actors with a potent way to initiate software supply-chain attacks. With dozens of third-parties already running on the average modern website, the security and compliance risks cannot be ignored anymore. You have to take care of your security blind spots to avoid becoming the next SolarWinds case.
Your third-party application code can allow unrestricted access to sensitive data, all at a browser level. This means that your traditional security tools cannot possibly meet the need. Think JavaScript library vulnerabilities, application backdoors, and other kinds of web-skimming attack variations.
Traditional AppSec tools are still helpful, but only complete and continuous monitoring of critical third-party web applications can truly secure your website. This will allow you to connect the dots and understand:
- What data is being used by your third-parties
- How they are using this data
- Which previously unknown fourth-party dependencies exist
- Any changes that happen, continuously
Get started now.
Subscribe to our newsletter
Stay updated with the latest news, articles, and insights from Reflectiz.
Your Website looks great!
But what’s happening behind the scenes?
Discover your website blind spots and vulnerabilities before it’s too late!