SOC 1 vs. SOC 2: What’s the difference and which one do you need?
The biggest challenge in a hyper-connected digital world is to secure data across various systems.
According to a report by Statista, in 2019 alone, the US recorded the theft of over 164.6 million user records from 1,473 cyber attacks. And with the number of data breaches increasing, guaranteeing air-tight data security seems like a superpower that most organizations only aspire to have. To ensure that organizations implement well-defined processes to safeguard their customer data, the American Institute of CPAs (AICPA) established guidelines or audit processes to certify businesses with credibility and generate System and Organization Controls (SOC) reports.
Though there are typically four types of SOC reports:
SOC 1, SOC 2, SOC 3, and SOC for Cybersecurity, SOC 1 and SOC 2 are the most commonly sought. So let’s take a deeper look at these two compliance reports and how they differ.
What is SOC 1?
Suppose you are a financial services organization or deal with users’ financial information.
In that case, SOC 1 (Service Organization Control 1) report certifies your capability to efficiently and securely manage your customers’ financial data.
Any organization that engages in payment processing, loan servicing, and other monetary transactions needs to get this certificate to document their business processes, and IT controls.
Previously known as SAS 70 (Statement on Auditing Standards 70), an internationally recognized third-party assurance audit, this attestation standard was replaced by the Statement on Standards for Attestation Engagements No. 16 (SSAE 16) audit, now simply called SOC 1.
The SOC 1 report focuses on controls ranging from password complexity to authorization restrictions. It also undertakes a few tests to identify vulnerabilities. It offers assurances concerning access to information or databases to restricted and authorized personnel.
SOC 1 reports are available in both Type 1 to highlight internal financial controls and Type 2, to emphasize the efficiency of the control over a time period.
If your organization is preparing for a SOC 1 audit, you must set your key control objectives. There are two kinds of objectives—one set for business operations, like customer data processing, and another set for IT methodologies to secure the data. You can use the SOC 1 report as evidence whenever someone questions your internal controls for payment processing and other security procedures.
A SOC 1 report consists of five parts, as explained below:
- Opinion Letter – This section includes the report’s scope, the date of the report for Type 1 attestation, the test period for Type 2 attestation, and the opinion of the auditors.
- Management’s Assertion – This is where the management’s statements are mentioned about the system’s description, control objectives, and the criteria used to make the assertions.
- Description of the System – This includes all your policies, processes, and operations that form your services and affect financial reporting.
- Description of Tests of Control & Result of Testing – This section is for the auditors to list the controls they have tested, the test procedure, and the results.
- Other Information – Auditors use this section to mention any essential information not covered in other areas of the report.
What is SOC 2?
SOC 2 report is proof that your organization has procedures in place to ensure security, integrity, and processing efficiency when dealing with sensitive customer information. This audit and requirement are necessary for technology-based companies that store customer data in the cloud. SOC 2 is the most common compliance that SaaS companies need today.
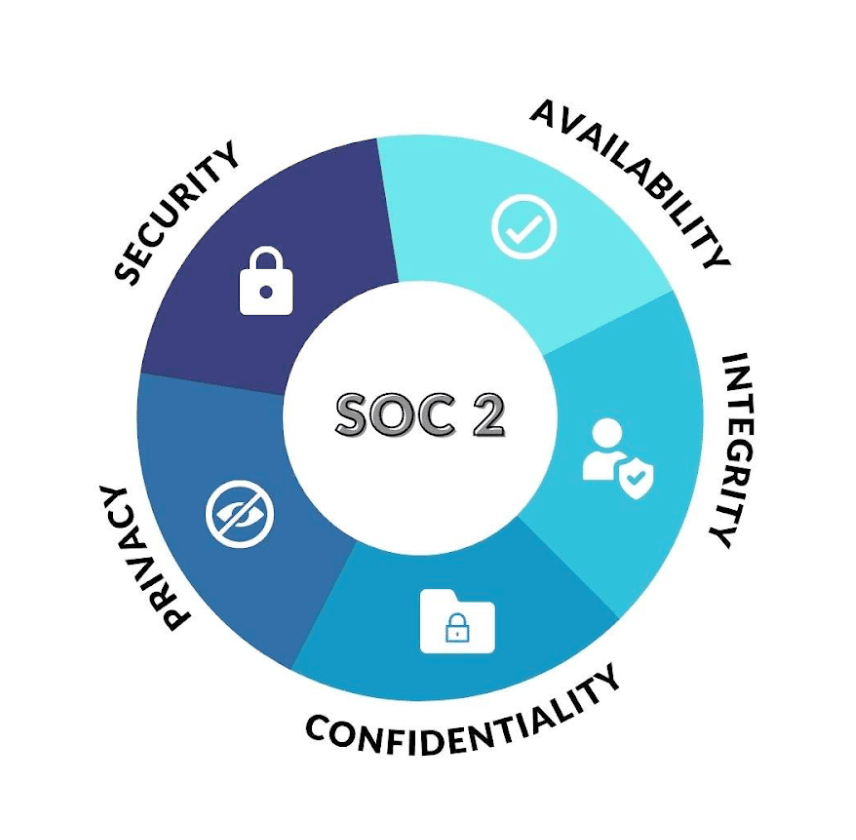
The SOC 2 report requires you to write down your security policy and follow it, which will be requested and reviewed at the time of auditing. The AICPA has outlined a set of Trust Service Criteria or Trust Service Principles to determine the trustworthiness of an organization’s data handling. The five criteria are as follows:
Security:
Safeguard data and systems against unauthorized access or any form of tampering activities
Availability:
Seamless availability of data and systems for business operations
Processing Integrity:
Accurate processing of data by authorized personnel in a timely manner
Confidentiality:
Appropriate guardrails and authentication mechanisms must be put in place for confidential data
Privacy:
Procedure to efficiently use, retain, and terminate personal information of any personnel
The SOC 2 is also available in both Type 1 and Type 2 reports, of which Type 1 is to disclose if your procedures and policies are trustworthy as to the specified data, and Type 2 is to highlight the system’s effectiveness over a time period.
You need to get a SOC 2 report if your organization collaborates with large enterprises that would want to verify your data handling efficiency.
SOC 1 vs. SOC 2: How different or similar are they?
If you’re unfamiliar with SOC auditing, selecting the right SOC compliance for your organization might seem like a task. It is fairly easy to get confused between SOC 1 and SOC 2 since both the reports pertain to an organization’s internal controls.
Also, SOC 2 is not an upgrade or a level-up of SOC 1.
Although both the compliance types evaluate the controls to protect sensitive customer information, they focus on different goals. In short, SOC 1 is ideal for organizations that deal with financial information and transactions, while SOC 2 is for technology organizations that handle customer data and to address cloud computing risks.
If your organization’s services assist in your customer’s financial activities like invoicing, collections, and claims settlement, you are directly affecting their financial reporting. In such scenarios, you must get a SOC 1 report. Also, if you are a publicly-traded company, you will need to get a SOC 1 report as part of the Sarbanes-Oxley Act (SOX).
In case your organization doesn’t process financial information but manages and processes other types of information, you must get a SOC 2 report. This compliance is to safeguard your organization from issues concerning regulatory, vendor management, and corporate governance.
It should also be noted that some organizations might need both SOC 1 and SOC 2 reports.
This is for businesses that span across industries and deal with customers for a wide variety of services, both financial and non-financial. In such cases, there could be the same tests mentioned in both reports.
Who should care about SOC compliance?
Most businesses do not need SOC compliance when they are first starting.
In general, SOC compliance is required in order to stand out in the marketplace and land more significant deals.
Ideally, customers should look to achieve SOC compliance before asking for the right to audit their systems.
Since a Type 2 audit requires evaluating a company’s environment over time, it is important to plan. Auditors won’t grant a compliance report until the six-month or yearlong audit period is complete, so it is important to start the process before you need to.
Why undergo a SOC audit?
A SOC report works as validation from an independent body regarding your organization’s processes and operational procedures to safeguard sensitive information.
It can also be asked as marketing merit to express your organization’s legitimacy and commitment to securing customer data. Also, one key benefit of undertaking a SOC audit is to detect gaps and security risks in your processes so that you can resolve them before any damage is done.
With the number of data breach incidents rising, users are skeptical of sharing their personal information with businesses. Emphasizing the SOC audit report could give them the much-needed confidence in handing you their confidential information.
How to become SOC compliant?
After determining the type of SOC report your business needs, you can start with a SOC Readiness Assessment. Independent CPAs (Certified Public Accountants) or any other accounting firms can undertake SOC audits as AICPA has a set of standards to outline the work of SOC auditors.
Although CPA organizations may hire non-CPA auditors for the process, they need to follow the predetermined set of guidelines to execute the process of evaluating the IT and business processes of an organization. Only the CPA can offer the final report, regardless of who conducts the audit.
Although pursuing SOC compliance reports is recommended, it is not a done deal from the security point of view.
It is critical to establish a defensive baseline and enforce security policies to protect your customer information efficiently.
Is SOC compliance the endgame?
SOC reports give organizations like SaaS companies, managed service enterprises, and data centers a stamp of approval for their commitment to data security.
It is a powerful recommendation and gives your business an edge against your competitors. These reports certify that you have zero security gaps.
However, cyber security management is a continuous process, which is why Reflectiz focuses on helping eCommerce and Financial Services organizations to seamlessly offer their services online by imposing industry-standard security measures and proactively mitigating risks. Instead of soft control and a mirage of security, Reflectiz gives you total control over your digital applications’ security and compliance management. Learn more about our enforcement capabilities here.
Subscribe to our newsletter
Stay updated with the latest news, articles, and insights from Reflectiz.
Your Website looks great!
But what’s happening behind the scenes?
Discover your website blind spots and vulnerabilities before it’s too late!