Evasive New Skimmer is Used to Attack Retail and Finance

How much do you know about the latest web-skimming attack against Magento? Reflectiz breaks down the key information, and explains how Magecart attacks have become increasingly sophisticated at stealing financial data from end-users.
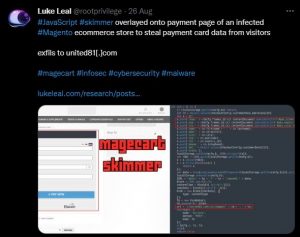
On August 26th, security engineer and researcher Luke Leal tweeted information about a Magento skimmer which was created by the Magecart group. The skimmer is live in the wild, and has been overlaid onto the payment pages of infected stores that leverage Magento to do business, a popular CMS used by more than a quarter of a million websites.
This attack is just another in a long list of examples of web skimming attacks that target retail and financial businesses. As Gulf Business reports, “Cybersecurity is now a c-level matter.”
Cybersecurity has become a strategic problem within organizations and it’s not enough to hire an IT team and expect that they can monitor and mitigate threats. Instead, top executives need to be aware, as well as take responsibility for prevention and mitigation.
How Does Web Skimming Against Financial Institutions Occur?
When web skimming hits retailers through payment pages on websites, the collateral damage is often the financial institutions and banks behind the transactions.
In this case, when a user visits a website compromised by vulnerabilities in the Magento software that is used behind the scenes, the overlay launches immediately, requesting that the customer enters their payment details. For the end-user, they would never know this isn’t a legitimate request from the vendor or retailer. Hackers then steal customers’ payment details directly from this overlay, after infiltrating the third-party vendor, usually via malicious code injection.
Data that can be stolen from this specific skimmer includes credit and debit card numbers, names, CVV numbers, and expiry dates. Everything an attacker needs to steal your customer identity, make fraudulent transactions, or sell on the profile on the Dark Web.
Of course, the customer is the main victim, as their data has been stolen, and the retailer is also heavily impacted — left with brand damage, loss of reputation, and regulatory hassle to contend with — but the invisible third victim in the equation is the bank or credit institution who is left with a claim for fraudulent transactions on their hands.
In some cases they are bound to return the stolen money to their consumers, but even when this isn’t the law, it leaves them with a conundrum on their hands. Do they reimburse the end-user and leave themselves out of pocket, or do they pass responsibility to the retailer and risk losing business from unhappy customers?
Mitigating Web Skimming Attacks with Reflectiz’ Unique Solution
The truth is, there is no obvious way for businesses to understand what’s happening on a third-party server. These risks are originating out of your area of control. While antivirus solutions might be able to pick up on brute force attacks or malware injection, a web skimming attack happens on the client side, which makes visibility almost impossible.
As well as a first line of defense that includes a CSP or a Web Application Firewall, today’s retailers need to implement a holistic solution that is built for the growing threat of web skimming, and closes the glaring gaps that occur when a business relies on traditional security tools alone.
A dedicated platform like Reflectiz provides a comprehensive view of all third party applications, offering a single pane of glass into which third and fourth parties have website access, what data they can reach, and where this data is being sent.
In this situation for example, if a web skimmer attempted to leverage the access that Magento has to your website environment, the unusual script activity would trigger an automatic alert, long before your customers’ data was at risk of being harvested for malicious intent.
Attacks against retailers are de facto attacks against financial institutions and banks. To protect your customers and your business, you need full visibility where it matters the most.
Interested in a solution that mitigates the risks of supply chain attacks, client-side injection and web skimming? Let’s schedule a demo and we can show you how it works.
Subscribe to our newsletter
Stay updated with the latest news, articles, and insights from Reflectiz.
Related Articles
Your Website looks great!
But what’s happening behind the scenes?
Discover your website blind spots and vulnerabilities before it’s too late!